Specialty Forensic Devices
Computer forensics and eDiscovery are complex fields and this complexity often demands the availability of specialized forensic tools. Digital Intelligence is intimiately familiar with these complex needs and specialized tools...In fact, we ourselves have created some of the specialized tools needed to address these needs.
Password Recovery
Encrypted evidence appears in more and more cases with each passing year. Fortunately there are specialized tools which make the recovery of encrypted evidence practical in a number of applications.
Software tools like Passware's Forensic Toolkit help automate the detection of encrypted evidence and - in many cases - can recover the passwords needed to access that evidence. For situations where password recovery is especially critical you can accelerate the password recovery process by adding specialized hardware like Comino's DPR.

Drive Enclosures
Computer forensics demands storage, lots of it. Frequently the most cost effective way to store evidence is on "bare" hard disks and you need drive enclosures to power, communicate with and protect those bare drives while using them. Digital Intelligence offers a specialized line of drive enclosures for these kinds of applications.
Drive Emulation
In special situations you may need to boot an evidence drive in its original computer. Normally you would never do this because the operating system will modify many files on the drive during the boot process - and of course that would compromise the evidence. Unfortunately, you can't use a normal write blocker in this situation because the operating system will likely fail to boot if it is unable to modify the drive.
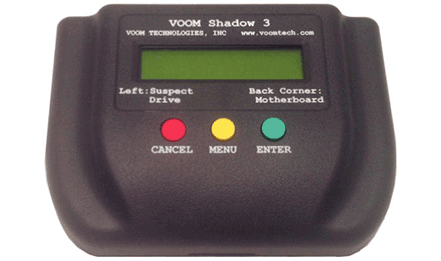
The solution is drive emulation. A special device like Voom's Shadow 3 sits "between" the evidence drive and the computer. When the computer tries to write to the evidence drive, the Shadow 3 intercepts the write requests and routes them to temporary storage, leaving the original evidence drive unmodified. The Shadow 3 keeps track of "modified" sectors (the ones written to temporary storage) so subsequent reading by the computer receives the correct data, either from the evidence drive or from the temporary drive. With this solution you can boot and use the original computer and evidence drive without making any permanent modifications to the evidence drive itself.

Technical Support You Can Count On
When you purchase from Digital Intelligence, you’re getting the best forensic products money can buy. But the value doesn’t stop there. You get lifetime technical support and access to a professional, dedicated support team. We measure our success not just by the number of systems we sell but also by the level of support we provide. Whether it’s a question about your FRED, UltraBlock, Imager or software – or a question about a forensic problem you face – we have your back. Call, email, or text. We are here for you.